Spanning Tree Protocol is one of the crucial mechanisms that keeps your network reliable and secure. STP protects your network against potential issues. It provides a blueprint for efficiently navigating within the network. In this blog, we will dig into the fundamentals of Spanning Tree Protocol and explore how it enhances network security.
What is Spanning Tree Protocol?
Spanning Tree Protocol, commonly referred to as STP, is a network protocol which operates at the Data Link Layer of the OSI model. It was initially standardized in the IEEE 802.1D specification and has since evolved with subsequent versions like Rapid Spanning Tree Protocol (RSTP) and Multiple Spanning Tree Protocol (MSTP).
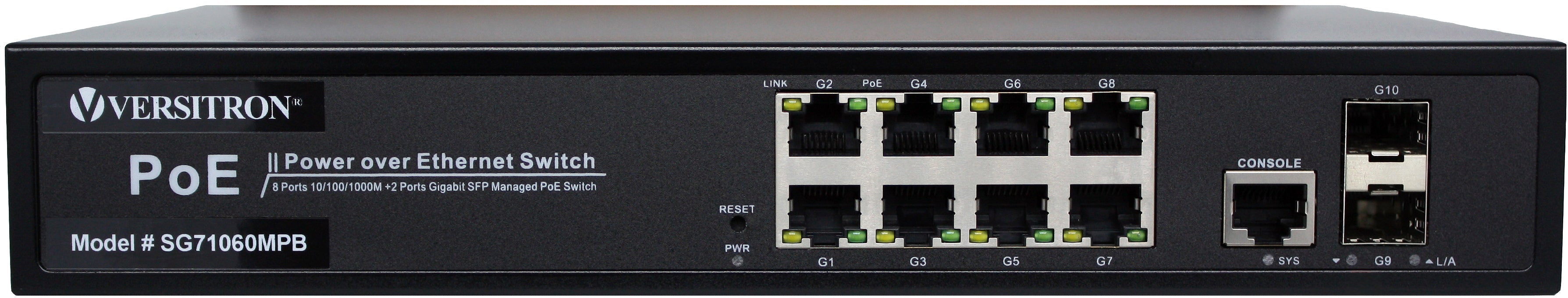
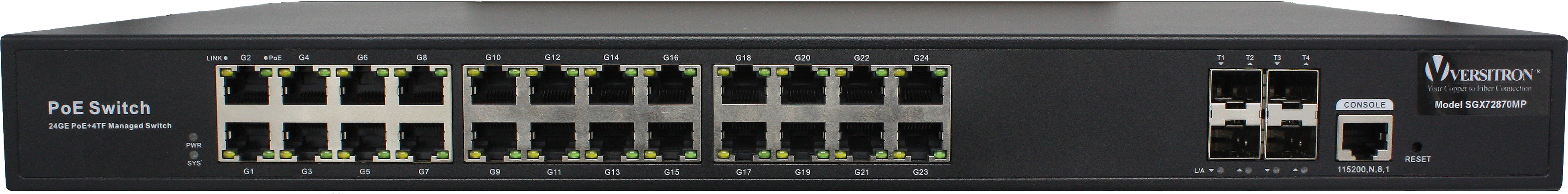
Spanning Tree Protocol is mostly found in industrial grade fully managed layer 2 switches. The primary objective of STP is to prevent the formation of loops in redundant network topologies. A loop occurs when there are multiple paths between network switches, causing packet collisions, broadcast storms, and severe network degradation. STP reduces this risk by regularly monitoring the network and selectively blocking redundant paths, hence establishing a loop-free logical topology.
Why do we need Spanning Tree Protocol?
We need Spanning Tree Protocol (STP) in computer networking to prevent network loops and ensure a stable and reliable communication environment within a Local Area Network (LAN). Here are the main reasons why STP is essential:
- Loop Prevention: Network loops occur when multiple paths exist between switches or network segments. If left unchecked, network loops can cause broadcast storms, wherein broadcast or multicast packets endlessly circulate the network, consuming bandwidth and causing network congestion. STP's primary function is to detect and eliminate network loops by creating a loop-free logical topology.
- Redundancy and High Availability: STP allows us to take advantage of redundant links while maintaining a loop-free topology. This ensures that if one link or switch fails, STP can rapidly and automatically reconfigure the network to use alternative paths, thus maintaining network connectivity.
- Traffic Optimization: By calculating the shortest path between switches, STP optimizes the traffic flow within the network. It selects the most efficient paths to forward data packets, reducing unnecessary delays and enhancing overall network performance.
- Plug-and-Play Capability: STP provides a plug-and-play capability, allowing network administrators to easily add or remove devices from the network without manual reconfiguration. STP automatically adjusts the network topology as devices are added or removed, reducing administrative overhead and simplifying network management.
- Compatibility with Ethernet Networks: STP is widely supported in Ethernet networks, making it a standard protocol for loop prevention. It is built into most network switches and routers, ensuring its compatibility across a wide range of networking equipment.
- Scalability: STP is scalable and can be used in networks of varying sizes, from small office LANs to large enterprise networks. It can handle complex network topologies and adapt to changes without requiring manual intervention, which is vital for managing large and dynamic networks effectively.
How does Spanning Tree Protocol work?
Spanning Tree Protocol is built on bridge protocol data units which are sent back and forth uses an algorithm called the Spanning Tree Algorithm (STA) for ensuring logical loop-free topology. Here's a simplified overview of how STP works:
- Electing a Root Bridge: In a network, one switch is elected as the Root Bridge, which serves as the reference point for determining the best paths to reach all other switches. The Root Bridge has the lowest Bridge ID, a combination of the Bridge Priority and the MAC address.
- Calculating the Best Path: Each switch, except the Root Bridge, determines the best path to reach the Root Bridge based on the cost associated with each link. The cost is typically determined by the link speed. Lower-cost paths are preferred.
- Blocking Redundant Paths: Once the best path to the Root Bridge is determined, STP selectively blocks redundant paths to prevent loops. Blocked paths remain inactive, acting as backups in case of a link failure.
- Port Roles: STP assigns specific roles to each port on a switch. These roles include,
- Root Port: the port closest to the Root Bridge
- Designated Port: the best path to reach a specific segment
- Blocked Port: inactive port to prevent loops
States of Spanning Tree Protocol (STP)
The STP (Spanning Tree Protocol) defines a series of stages or states that a network switch port goes through during the process of creating a loop-free logical topology within a local area network (LAN). The main objective of STP is to prevent broadcast storms and the formation of network loops, which could lead to excessive traffic and network outages. The STP Port States stages of the STP Protocol are as follows:

- Blocking State: The switch port does not participate in the data forwarding process. It listens to network traffic to learn about the network topology and gathers information about other switches and ports.
- Listening State: The switch port begins to actively participate in the STP protocol by sending and receiving BPDU (Bridge Protocol Data Unit) messages. The port does not forward data frames during the listening stage.
- Learning State: The port continues to listen for BPDU messages and starts to learn the MAC addresses of devices connected to the network. However, the port still does not forward data frames during the learning stage.
- Forwarding State: The port actively participates in the data forwarding process. It forwards data frames between connected devices and actively contributes to the network communications. The forwarding state is the normal operational state for a switch port, allowing the network to function properly while maintaining a loop-free topology.
- Disabled State: A type of state that is not involved in the spanning Tree loop is known as a Disabled State. The port is administratively disabled, and also it has unlimited timing so this state does not participate in the spanning tree loop.
What are the Types of Spanning Tree Protocol?
Over the years, there is rise in different variations of STP that offer enhanced functionality and improved performance. Following are the types of STP in networking which are commonly used:
-
IEEE 802.1D Spanning Tree Protocol (STP):
- The IEEE 802.1D STP is the original and most basic version of STP.
- It uses the Spanning Tree Algorithm (STA) to elect a Root Bridge and calculate the best path to reach the Root Bridge from each switch.
- However, IEEE 802.1D STP has slower convergence in larger networks.
-
Rapid Spanning Tree Protocol (RSTP):
- Rapid Spanning Tree Protocol is the improved version of STP
- It reduces the convergence time in response to network changes, such as link failures or additions.
- Fast convergence is achieved by introducing new port states and mechanisms like the Alternate Port and Backup Port.
- RSTP allows seamless integration with existing networks.
-
Multiple Spanning Tree Protocol (MSTP):
- Multiple Spanning Tree Protocol extends the functionality of STP by to create multiple spanning trees within a network.
- For designing complex networks, MSTP provide flexibility.
- MSTP reduces the computational burden on switches and enhances network performance.
-
Per-VLAN Spanning Tree Plus (PVST+):
- PVST+ is a Cisco proprietary extension of STP that provides a separate spanning tree for each VLAN in the network.
- It allows more granular control over spanning tree configurations at the VLAN level, enabling optimized forwarding paths for individual VLANs.
- PVST+ maintains compatibility with IEEE 802.1D STP and allows Cisco network devices to interoperate seamlessly with non-Cisco devices using standard STP.
-
Rapid PVST+:
- Rapid PVST+ is an enhancement of PVST+.
- It provides fast convergence times by utilizing the rapid spanning tree techniques for each VLAN.
- RPVST+ is commonly used in Cisco networks to achieve faster network recovery in VLAN-based environments.
Differences between STP and RSTP:
Spanning Tree Protocol (STP) and Rapid Spanning Tree Protocol (RSTP) are both network protocols used to prevent network loops and ensure a loop-free topology in Ethernet networks.
However, RSTP is an improvement and enhancement over STP, offering faster convergence and additional features. Here are the key differences between STP and RSTP:
| Spanning Tree Protocol (STP) | Rapid Spanning Tree Protocol (RSTP) | |
|---|---|---|
| Convergence Time | Slow convergence. Typically taking up to 30 to 50 seconds to reconfigure the network | Rapid convergence. Usually within 1 to 3 seconds. |
| Port States | STP operates with three port states: Blocking, Listening, and Learning before reaching the Forwarding state. | RSTP introduces additional port states: Discarding and Learning. |
| Bridge Roles | STP defines a single Root Bridge for the entire network, and other switches act as either Designated or Non-Designated Bridges. | RSTP introduces the concept of Backup and Alternate Ports, which further enhances redundancy and load balancing in the network. |
| Topology Changes | STP goes through a full recalculation, causing network-wide convergence delays. | RSTP handles topology changes locally on the affected switch, using the synchronization of BPDUs (Bridge Protocol Data Units) to quickly converge the network. |
| Backward Compatibility | STP is not backward compatible with RSTP. | RSTP is backward compatible with STP. |
Enhancing Network Security through Spanning Tree Protocol:
Beyond its primary role of ensuring network stability by eliminating loops, Spanning Tree Protocol also contributes to network security in the following ways:
- Preventing Broadcast Storms: By blocking redundant paths, STP prevents the spread of broadcast storms, which can overwhelm the network and compromise its security and performance.
- Controlling Unauthorized Network Access: STP allows network administrators to control which ports are active and which are blocked. This capability aids in preventing unauthorized devices from connecting to the Ethernet network by blocking unused or unauthorized ports.
- Detecting and Responding to Network Changes: STP continuously monitors the network for changes such as link failures, additions, or removal of switches. When a change occurs, STP recalculates the best path and adapts the network accordingly, ensuring uninterrupted connectivity and enhancing the network's resilience to security threats.
Conclusion:
Spanning Tree Protocol is a vital network protocol that not only ensures the stability and reliability of a network but also contributes to network security. By preventing loops, controlling network access, and responding to changes, STP creates a secure environment for data transmission and protects against potential network vulnerabilities. Understanding the inner workings of Spanning Tree Protocol enables network administrators to design robust, secure networks that meet the demands of today's interconnected world. Versitron is a leading provider of network connectivity solutions, including a range of layer 2 managed switches, PoE Switches, media converters that are designed to provide reliable and cost-effective connectivity for your networks.
FAQs
The STP bridge that serves as the basis for all path calculations is the "Root Bridge”. The "Root Bridge" in STP is the switch with the lowest Bridge ID and serves as the central reference point for path calculations in the network.
The Spanning Tree Protocol (STP) addresses the potential issue of network loops caused by redundant connections in a networking environment, preventing broadcast storms and ensuring a loop-free logical topology.
The Spanning Tree Protocol (STP) can be used to prevent looping and broadcast storms in a network. It works by creating a loop-free logical topology, selecting a Root Bridge, and blocking redundant connections, ensuring data packets follow efficient paths without causing loops or flooding the network with unnecessary broadcast traffic.
Spanning" refers to the process of creating a loop-free logical topology for an Ethernet network.
The Spanning Tree Protocol (STP) helps to ensure that you will have a loop-free Ethernet network when connecting multiple switches with redundant links. STP blocks certain redundant connections and creates a loop-free logical topology, preventing network loops and ensuring efficient data transmission.
The function of STP in a scalable network is to allow the implementation of Layer 2 devices without forming Layer 2 loops in redundant physical connections.